We are here to help
Navigating the maze of cybersecurity can be daunting.
Selecting the optimal cybersecurity solutions can be a challenging task, especially for IT consultants who are still gaining experience. Fortunately, at UB Computers, you have access to a team of seasoned professionals. Our experts have been at the forefront of the IT industry for over 34 years, contributing significantly to the development and evolution of the cybersecurity landscape as we know it today. We encourage you to leverage our extensive experience and expertise for your cybersecurity needs. Feel free to reach out to us at any time; we're here to assist you.
So Many choices
Selecting the optimal cybersecurity solutions can be a challenging task, especially for IT consultants who are still gaining experience. Fortunately, at UB Computers, you have access to a team of seasoned professionals. Our experts have been at the forefront of the IT industry for over 34 years, contributing significantly to the development and evolution of the cybersecurity landscape as we know it today. We encourage you to leverage our extensive experience and expertise for your cybersecurity needs. Feel free to reach out to us at any time; we're here to assist you.
Overlaping Features
Selecting the optimal cybersecurity solutions can be a challenging task, especially for IT consultants who are still gaining experience. Fortunately, at UB Computers, you have access to a team of seasoned professionals. Our experts have been at the forefront of the IT industry for over 34 years, contributing significantly to the development and evolution of the cybersecurity landscape as we know it today. We encourage you to leverage our extensive experience and expertise for your cybersecurity needs. Feel free to reach out to us at any time; we're here to assist you.
How we handle it.
Selecting the optimal cybersecurity solutions can be a challenging task, especially for IT consultants who are still gaining experience. Fortunately, at UB Computers, you have access to a team of seasoned professionals. Our experts have been at the forefront of the IT industry for over 34 years, contributing significantly to the development and evolution of the cybersecurity landscape as we know it today. We encourage you to leverage our extensive experience and expertise for your cybersecurity needs. Feel free to reach out to us at any time; we're here to assist you.
- A server/browser tries to connect to an SSL-secured website.
- The server/browser requests that the website identifies itself.
- The web server responds by sending a copy of its SSL certificate.
- The server/browser checks the certificate to see whether it is trusted. If yes, it signals this to the website.
- The website returns a digitally signed acknowledgment to start an SSL- encrypted session.
- The two parties share the encrypted data.

WatchGuard
WatchGuard Firebox is a comprehensive advanced network security appliance that puts IT security professionals back in charge of their networks with widely deployable, enterprise-grade security and threat visibility tools suitable for any organization, regardless of budget, size, or complexity.
Protect Your Network with Security Services.
A Package for Every Level of Security
All WatchGuard appliances come standard with a Support license that includes full VPN capabilities and built-in SD WAN. Looking for more? Choose our Basic or Total Security Suite:
Basic Security Suite
The Basic Security Suite includes all of the traditional network security services typical to a UTM appliance: IPS, antivirus, URL filtering, application control, spam blocking and reputation lookup. It also includes our centralized management and network visibility capabilities, as well as our standard 24x7 support.
Total Security Suite
The Total Security Suite includes all services offered with the Basic Security Suite plus AI-powered malware protection, enhanced network visibility, endpoint protection, Cloud sandboxing, DNS filtering, and the ability to take action against threats right from WatchGuard Cloud, our network visibility platform.
Get it all with the Total Security Suite
Find out which fits the needs of your network. Designed for maximum protection against sophisticated threats, our security services are packaged to take the guesswork out of network security.
| SUPPORT | BASIC SECURITY | TOTAL SECURITY | |
|---|---|---|---|
| Stateful Firewall | |||
| VPM | |||
| SD-WAN | |||
| Access Portal* | |||
| Intrusion Prevention Service (IPS) | |||
| Application Control | |||
| WebBlocker | |||
| spamBlocker | |||
| Gateway AntiVirus | |||
| Reputation Enabled Defense | |||
| Network Discovery | |||
| APT Blocker | |||
| DNSWatch | |||
| IntelligentAV** | |||
| ThreatSync (XDR) | |||
| EDR Core | |||
| WatchGuard Cloud Log Data Retention Report Data Retention | 90 Days 1 Day | 365 Days 30 Days | |
| Support | Standard (24x7) | Standard (24x7) | Gold (24x7) |

Protection for the future, present and past
Businesses require protection against today’s most sophisticated cybersecurity threats without unnecessary complications. Let VIPRE help keep your organization safe from online threats and data risks with customizable solutions.
Endpoint Security

ENDPOINT DETECTION & RESPONSE
Powerful EDR without the complexity Detect and respond instantly to endpoint threats with next-generation EDR and antivirus technology built for SMEs and the partners that serve them.
ENDPOINT MANAGED DETECTION & RESPONSE (MDR)
24x7x365 threat monitoring & incident coverage Gain peace of mind with VIPRE Endpoint MDR – the wrap-around service for VIPRE Endpoint Detection & Response (EDR).
ENDPOINT SECURITY CLOUD
Next-Gen Antivirus for Advanced Malware Protection Consistently ranked in the top 5 for efficacy in independent testing, VIPRE Endpoint Security Cloud delivers nextgen antivirus protection and convenience.
ENCRYPT.TEAM
Secure Your Remote Workforce Simplify secure access to local networks, cloud infrastructures and business applications, with one united platform. Keep employees safe online while working remotely or on-the-go.
Email Security
ATP – EMAIL SECURITY ADVANCED THREAT PROTECTION
Protection for the future, present and past Future proof email security for your most vulnerable business application.
EMAIL SECURITY CLOUD
Protect your business from the #1 cyber attack vector Get unparalleled protection against malicious links and infected attachments
SAFESEND
Prevent sensitive emails from being sent to the wrong person Confirm external recipients and attachments with a convenient Outlook add-in
EMAIL ARCHIVING
Take Control of your Email Archiving Take control of your Email with VIPRE Email Archiving: The Powerful, Fast & Secure Email Archiving Solution.
Threat Intelligence
Detect, analyze and destroy persistent threats
THREATANALYZER
Analyze potential malware, cyber threats with ThreatAnalyzer Leverage machine learning to conduct a deep analysis of discovered potential threats
THREATIQ
Detect and stop threats on your network with ThreatIQ Real-time intelligence stream to strengthen your cybersecurity and stop attackers cold. Now you can fight back before they strike.

Everything you need to protect your data
Secure Backup & Fast Recovery
- Fast, application‑aware, image‑based backups for VMware, NAS, Windows and more!
- Native backup and recovery for AWS, Azure and Google Cloud
- Bulletproof ransomware protection with immutable backups functionality
- Achieve data retention goals without blowing up your monthly bill
Proven Recovery Orchestration
- Get sub-minute RPOand fail over to the latest state instantly withVeeam CDP
- Immediate recoveryand production data access for VMs, entire NAS shares and SQL/Oracle databases with Instant Recovery®
- 1-click site recovery and DR testing withVeeam Recovery Orchestrator
Proactive Monitoring & Analytics
- Fast, application‑aware, image‑based backups for VMware, NAS, Windows and more!
- Native backup and recovery for AWS, Azure and Google Cloud
- Bulletproof ransomware protection with immutable backups functionality
- Achieve data retention goals without blowing up your monthly bill
Virtual Tech
Welcome to the future and let me introduce you to virtual tech. The virtual tech that lives inside your computer 24 hours a day to keep your network and computers functioning the best they can. She is a team player and has become an integral part of the U&B team. Let us put her to work for you.
 Remote monitoring
Remote monitoring
The monitoring aspect will allow the RMM tool to analyze events on the computer. Errors in Windows event logs, high CPU usage, high RAM usage, blue screen errors, etc. This will allows us to detect system problems BEFORE a major problem happens. This way we can proactively address systems before major problems occur.
 Patch Management
Patch Management
The Patch Management is where it gets good. This is a MUST to maintain security across all of our customers computers and servers. I have discovered it is simply not sufficient to rely on Windows updates to make sure systems are fully patched and patched in a timely fashion. With the patch management feature the RMM tool will monitor each of the systems and install updates/patches based on a schedule that we define. For example we can install critical updates within a few days of release and standard updates less often (weekly, monthly, whatever we decide is relevant). In addition, if there is a report of a “bad” update, we can exclude those updates in the RMM tool to avoid problems before they happen. With the increase in ransomware viruses attacking non-updated systems, this is a great thing to have.
 Why are you waiting
Why are you waiting
Call Now 734-765-3483
Access Security for Everyone, from Any Device, Anywhere
For organizations of all sizes that need to protect sensitive data at scale, Duo is the user-friendly zero trust security platform for all users, all devices and all applications.
Your Journey to Zero Trust Starts Here
Zero trust takes security beyond the corporate network perimeter, protecting your data at every access attempt, from any device, anywhere. It's the future of information security — and Duo is your rock-solid foundation.
Verify User Trust
Ensure users are who they say they are at every access attempt, and regularly reaffirm their trustworthiness.
Establish Device Trust
See every device used to access your applications, and continuously verify device health and security posture.
Enforce Adaptive Policies
Assign granular and contextual access policies, limiting exposure of your information to as few users and devices as possible.
CISCO DUO
Lets see if it's right for you - 734-765-3483

SSL Certificate
You would not want to give the keys to a stranger, Your computer does not want to either.
Stay Safe
What Is an SSL certificate?
An SSL (Secure Sockets Layer) certificate is a digital certificate that verifies a website’s identity and allows an encrypted connection between servers and browsers. A padlock icon next to the site’s URL in the address bar indicates SSL protection.
Why Do You Need an SSL Certificate?
Companies and businesses need to add SSL certificates to their sites to secure online transactions and secure customers’ PII (Personal Identifiable Information). The protocol prevents criminals from modifying or reading private information during transit between systems.
The SSL certification protocol was created around 25 years ago. There have been several SSL versions, with the latest being TLS (Transport Layer Security). However, it is still called SSL.
How Does SLL certification work?
The SSL process, also called an “SSL handshake,” ensures that data in transit between users and sites or two systems is impossible to read. Data often includes personal information, such as names, credit card numbers, and addresses. Therefore, using encryption algorithms to scramble data prevents hackers from examining it as it passes over the connection. It may sound like a long process; however, SSL takes less than seconds.
The process is as follows:
- A server/browser tries to connect to an SSL-secured website.
- The server/browser requests that the website identifies itself.
- The web server responds by sending a copy of its SSL certificate.
- The server/browser checks the certificate to see whether it is trusted. If yes, it signals this to the website.
- The website returns a digitally signed acknowledgment to start an SSL- encrypted session.
- The two parties share the encrypted data.
How to Check For An SSL Certificate
When a site is SSL-certified, the acronym in the URL is HTTP (HyperText Transfer Protocol Secure). If there is no SSL, the URL letters are just HTTP (no ‘S’ for Secure). Also, there should be a padlock icon next to the URL in the address bar. The icon offers reassurance that you can trust the site you are visiting.
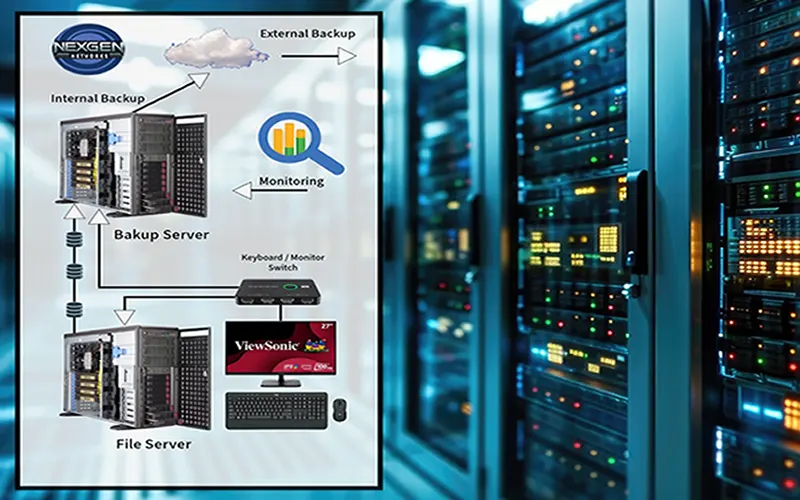
Backup
In today's digital age, data is one of the most valuable assets for both individuals and businesses. The importance of regular backups cannot be overstated, as they are a critical line of defense against data loss. Whether it's due to hardware failure, cyber-attacks, accidental deletions, or natural disasters, losing data can have catastrophic consequences. Regular backups ensure that your data is preserved and can be quickly restored, maintaining business continuity and safeguarding personal memories.
Diverse Methods of Data Backup:
Cloud Backup
Cloud backup services offer a convenient and reliable way to store data remotely. By regularly uploading your data to a cloud server, you ensure that it's accessible from anywhere and protected against physical damage to your local devices.
External Hard Drives
Using external hard drives for backup provides a straightforward and cost-effective solution. It's advisable to keep these drives in a secure location separate from your primary device to protect against theft or physical damage.
Network-Attached Storage (NAS)
Using external hard drives for backup provides a straightforward and cost-effective solution. It's advisable to keep these drives in a secure location separate from your primary device to protect against theft or physical damage.
USB Flash Drives
Using external hard drives for backup provides a straightforward and cost-effective solution. It's advisable to keep these drives in a secure location separate from your primary device to protect against theft or physical damage.
Automated Backup Software
Implementing automated backup software can streamline the process. These programs regularly back up your data without manual intervention, ensuring that your latest data is always secure.
The Solution
Combination of 2 bla bla bla ....
Remember, regular backups are not just a safety measure; they are an investment in your peace of mind and the longevity of your valuable data.

Backup
In today's digital age, data is one of the most valuable assets for both individuals and businesses. The importance of regular backups cannot be overstated, as they are a critical line of defense against data loss. Whether it's due to hardware failure, cyber-attacks, accidental deletions, or natural disasters, losing data can have catastrophic consequences. Regular backups ensure that your data is preserved and can be quickly restored, maintaining business continuity and safeguarding personal memories.
From Home PC, Office Workstation, File Server To Rack Equipment
Protect valuable electronics
Weather events have been increasing in number and impact over recent years. While we can’t help you save that precious family heirloom or photo album, we can help you protect those important home electronics that we all rely on throughout our daily lives.
Why do you need power protection
Weather events can cause power outages, some lasting an extended period of time as well as power spikes and surges. These power problems can damage sensitive electronic equipment. During these extreme events, it's more important than ever to stay connected to work, family, and friends and entertainment. A battery backup or uninterruptible power supply (UPS) can help you weather the storm.
Home Protection Solutions
From surge protection to an uninterruptible power supply (UPS0, APC is a wide variety of solutions to help you prepare for and protect you from the damage effects of a problem resulting from a weather event.